Create and configure a test client
To test our example, we generate a test client, etest.Finally, generate a server-locked profile. The profile will be stored in For generating an auto-login profile:
etest.ovpn:Shell
Shell
Install the profile and certificate in OpenVPN Connect v3
Simplified ePKI client configuration (Access Server 2.14.2 and later)
With the release of Access Server 2.14.2, we’ve made configuring client connection profiles for ePKI easier. Previously, creating these profiles required using the command line, as noted in the tutorial. However, in version 2.14.2 and later, you can now create and manage ePKI client connection profiles directly from Access Server’s Client Web UI. There are two types of ePKI profiles available:-
Generic ePKI profile:
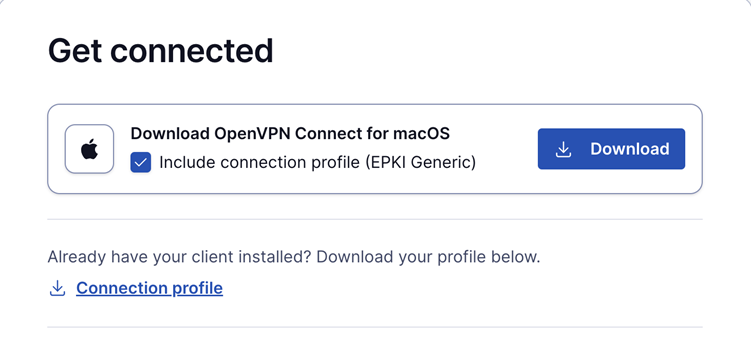
- This profile requires the user to authenticate with a password when connecting.
- Ideal for environments where a password-based security layer is needed in addition to certificate-based authentication.
-
Auto-login ePKI profile:
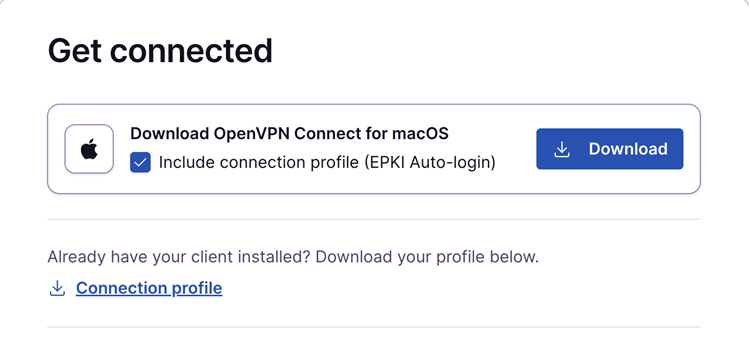
- This profile automatically uses the certificate for authentication without requiring a password.
- Suitable for unattended devices or systems where automatic, certificate-based login is needed.

